Read-Only Collection as an Audit Boundary
Why MAS TRM-inspired automation should observe systems before trying to fix them.
Most compliance automation fails in a quiet way.
The collector changes the system it is supposed to observe.
A playbook checks a setting and updates it.
A script gathers evidence and restarts a service.
A compliance job produces a clean result after it has already changed the target.
That may help operations. It weakens audit evidence.
The audit problem starts earlier than reporting. It starts at collection.
If collection changes the target, the evidence has already lost part of its value. You are no longer recording system state. You are participating in it.
That is why read-only collection is not a convenience. It is an audit boundary.
MAS TRM-inspired does not mean MAS TRM-prescribed
This series is inspired by MAS TRM, but it is not a legal reading of MAS TRM.
MAS TRM does not prescribe this pipeline. It does not require Ansible, SHA256, Python, OPA, or any specific collector. The point is narrower than that.
I use MAS TRM as an engineering pressure test.
If a control needs assurance, what evidence would support that assurance?
If evidence must be trusted, how should it be collected?
If system state matters, how do we observe it without contaminating it?
That is the boundary.
MAS TRM gives principles and expectations. The pipeline is an engineering interpretation of those expectations around control assurance, evidence protection, monitoring, and cryptographic lifecycle management.
The broader argument of this series is simple: compliance automation should move away from report production and toward evidence systems.
This article focuses on the first boundary in that shift.
Collection is not correction.
Observation is not remediation
These two actions are often mixed because the same tool can do both.
That is exactly the problem.
Observation asks: what is true now?
Remediation asks: what should we change?
They are not the same workflow.
If a playbook checks a TLS configuration and then fixes it in the same run, what does the evidence prove? Did the system meet the requirement before the collector ran, or only after the automation changed it?
That ambiguity is not cosmetic. It changes how much trust the evidence deserves.
Reports persuade. Evidence survives.
A read-only collector gives you a cleaner line:
this is what was observed
this is when it was observed
this is how it was collected
the collector did not modify the target system
That is a defensible starting point. A post-remediation snapshot is not the same thing.
Data alone is not evidence
A raw command output is data.
A screenshot is data.
A JSON file without provenance is data.
Data becomes audit evidence only when collection context is preserved.
A minimum evidence object should carry collector metadata, not only system facts:
{
"host_id": "apache-01",
"collector": "ansible-readonly-http-collector",
"collector_version": "0.1.0",
"timestamp_utc": "2026-05-05T10:30:00Z",
"evidence_type": "http_tls_configuration",
"data": {}
}
These fields are not decoration. They answer later questions: which host produced this evidence, which collector shaped the output, which collector version was used, when the evidence was collected, and what system state the record describes.
Without those answers, evidence becomes easy to dispute and hard to replay.
Integrity comes after observation
Once evidence is collected, it should be sealed before interpretation.
That seal can be simple at the first stage: timestamp the evidence package, calculate a hash over the complete object, and verify the hash before policy evaluation.
The goal is not cryptographic theatre. The goal is audit discipline.
OPA belongs after this step. It can evaluate verified evidence against explicit rules. It should not be asked to compensate for weak collection design.
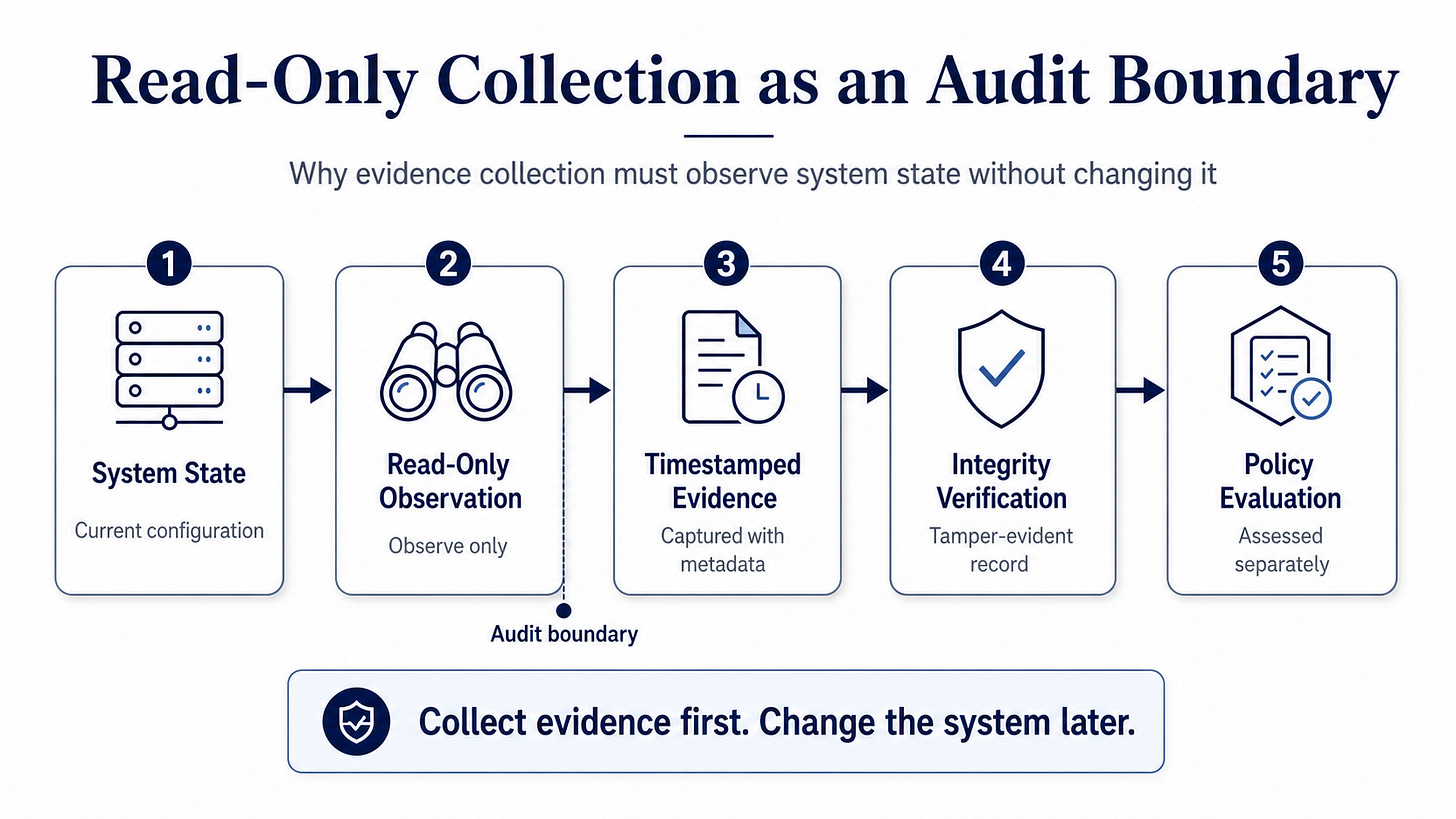
The order matters:
System State
→ Read-Only Observation
→ Timestamped Evidence
→ Integrity Verification
→ Policy Evaluation
Collection observes.
Integrity verification protects the observation.
Policy evaluation applies control logic.
Do not collapse these stages into one automation run and call it assurance.
Remediation belongs elsewhere
Read-only collection does not mean remediation is unimportant.
It means remediation needs its own workflow.
A change workflow should have its own approval record, execution trace, rollback path, and post-change verification. It may use Ansible. It may use a ticketing system. It may use CI/CD. It may use another control plane.
But it should not be hidden inside the evidence collector.
Collection is evidence work.
Remediation is change work.
Different evidence. Different accountability. Different audit story.